In the first part of this series I explained and demonstrated the process how non-programmable TOTP tokens can be used as a possible alternative to the Microsoft Authenticator app. In this second post I will cover programmable tokens. Non-programmable tokens are simple to use because the secrets are pre-loaded onto the tokens and cannot be changed. But at the same time that also means, that another party – the token vendor – knows your secrets. Using programmable tokens, this can be changed because it’s now you that loads the secrets onto the tokens. And they offer some more flexibility and configuration options based on your exact needs
- Part 1/2: Non-Programmable Tokens
- Part 2/2: Programmable Tokens (this post)
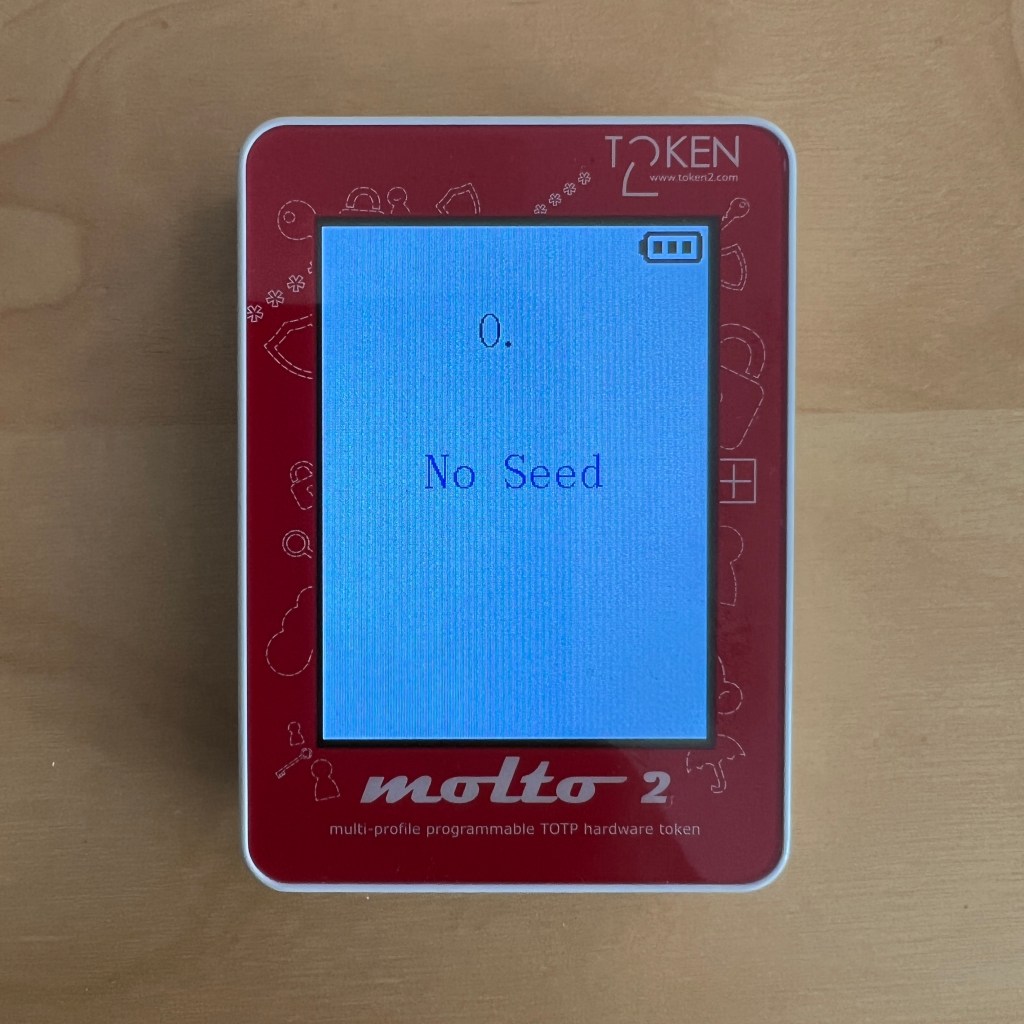
For this post I will use a programmable token from Token2 that allows up to 100 seeds/profiles – the Molto-2. This is great in case a person needs codes for multiple accounts – more or less the same convenience that the Microsoft Authenticator app offers. You can load tokens for various platforms such as Microsoft Azure AD, Google and more.
To load the seeds onto the token I will connect the device using USB and download the Molto-2 app. Depending on the token, other methods might be offered (such as NFC using specific token burner apps).
Molto-2 Configuration Tool
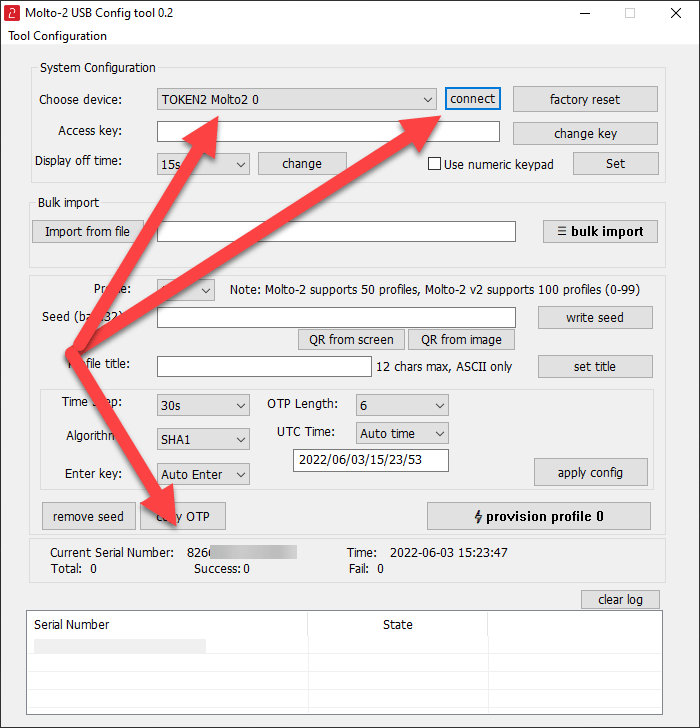
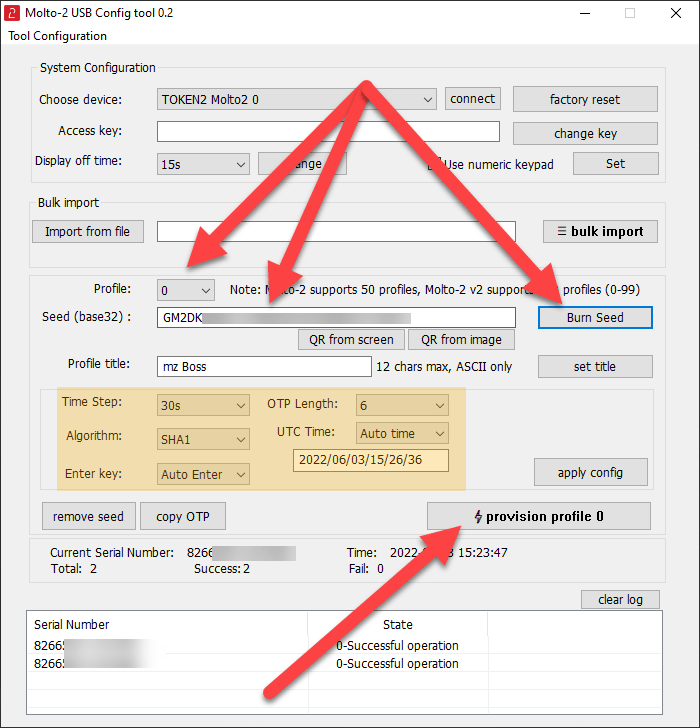
After downloading and starting the configuration app, I need to connect it to the USB-attached Molto-2. This loads some token details such as the serial number.
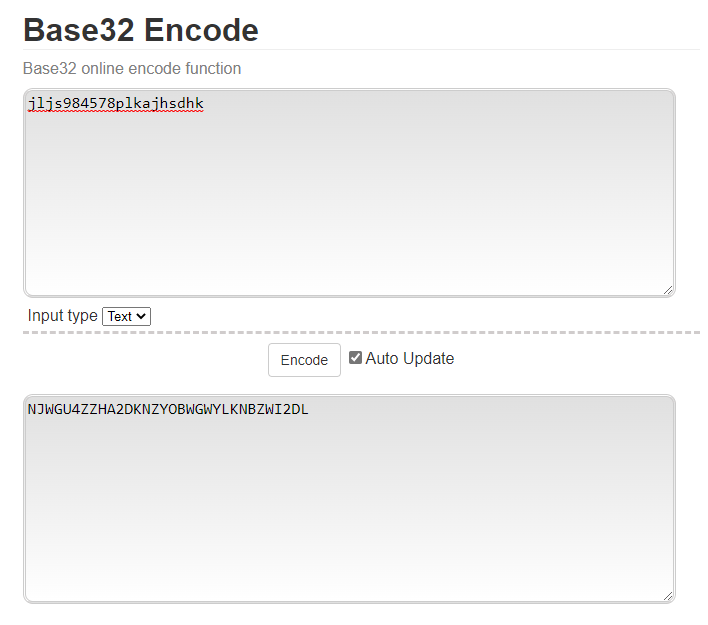
Now, I need to have a Base32-encoded value ready that will be used as a seed. This can be generated using a variety of methods such as using a PowerShell function or one of the available online encoding tools. One example of such a tool is this one. Just enter some characters and the encoded value will be shown.
In the token configuration app I now select the first profile (slot) I want to use (0) and then paste the generated Base32-encoded value. After that, the seed can be burned to the device. When other changes are needed, such as the algorithm, OTP length or interval, these values can be changed as needed. Finally, the profile is provisioned to the device. If multiple profiles are needed, I just select another profile slot, set another seed and provision that profile too. In this example, I provisioned a total of 3 profiles that I want to use for 3 different accounts onto the same token.
After at least 1 profile has been provisioned, the token now shows the current code. Using the buttons at the top of the device I can navigate between all available profiles.
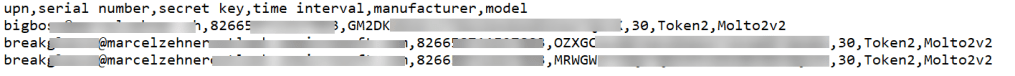
Import to Azure AD
Now it’s time to make Azure AD aware of that token and it’s profiles. I already explained the import and activation process in part 1, so I will go into the details here again. Just 1 thing: Because our token stores multiple profiles (each profile for another user account), I need to import each profile separately into Azure AD. So the CSV-file for this example will contain 3 entries, all referencing to the same token, but each one using its own seed and having its own assigned user account.
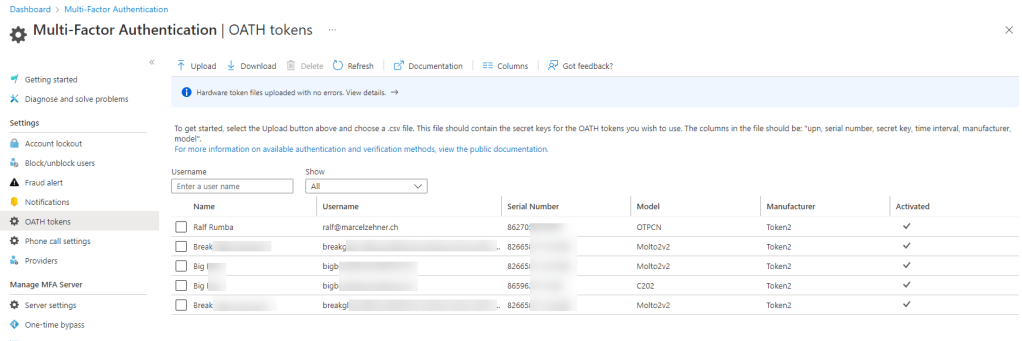
After a successful import, I now see 3 tokens (knowing all are actually on the same device). Each token needs to enabled separately for the various users. The use of the tokens is exactly the same as shown in part 1.
And that’s it. Means, if you are in need of more control of your tokens, maybe programmable tokens are the way to go. Have fun trying out!
Cheers
Marcel






Pingback: Using TOTP Tokens with Azure AD – Part 1/2: Non-programmable Tokens | marcelzehner.ch